While Cyberattacks Are Inevitable, Resilience Is Vital
This process can introduce a pragmatic, trust-but-verify (peer review and CER) culture into the OT cybersecurity solution development, explained Gunter. Industrial OT cybersecurity maturity will benefit from interactions with other professionals, consultants and service providers to validate technology, trends, skills, work processes and approaches,” he added.
Over the past 15 years, OT defenses have gotten better and stronger, but there needs to be a constant state of vigilance. “Increased focus on OT assets has improved overall cybersecurity,” Carrigan said. “Industry and regulatory bodies realize OT systems are essential to delivering critical services and products and have increased investments to secure these assets.
In general, Carrigan added, “investments in segmentation, threat detection and remediation, asset management, and basic hygiene have improved our security posture. That said, while we have improved our ability to prevent and detect events, there needs to be more investment to respond and recover.”
OT protection fundamentals
In the spirit of applying fundamental cybersecurity practices for OT, Chowdhury offered a range of practical suggestions.
Network segmentation: Network segmentation protects OT assets effectively. Existing technologies support VLANs to carve out the network, or modern firewalls create zones to separate OT equipment. During a cyber breach, segmentation prevents attackers from accessing other parts of the network, confining them to a specific zone. This confinement facilitates quicker detection and response. Situational awareness in OT networks is simpler compared to corporate IT environments because OT networks are predictable. Attackers on a segmented network trigger multiple alarms when they attempt to access different networks or unusual ports.
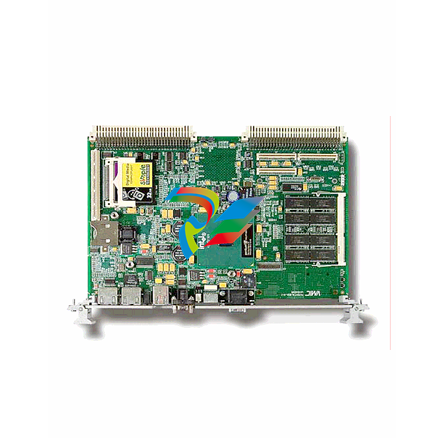
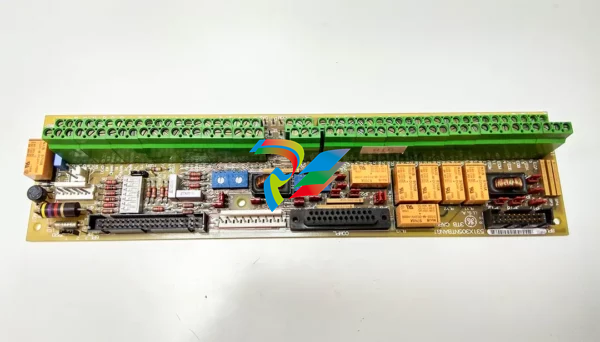
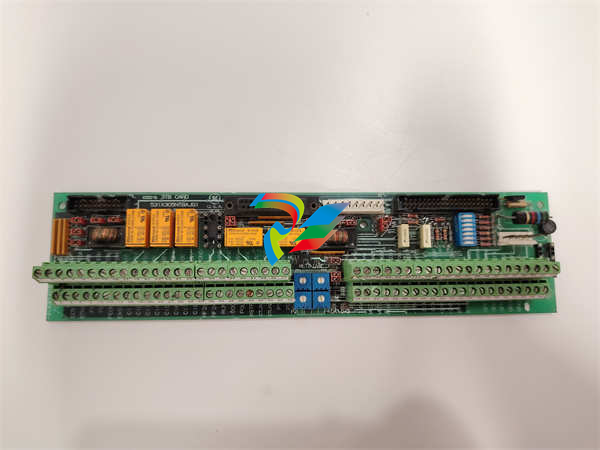
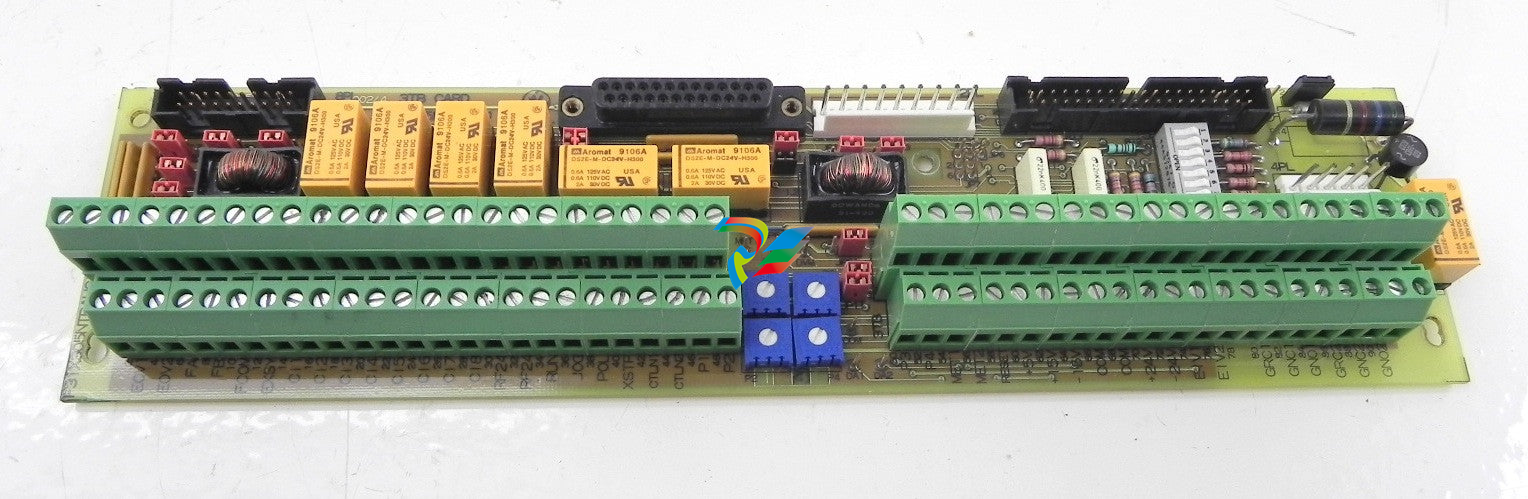
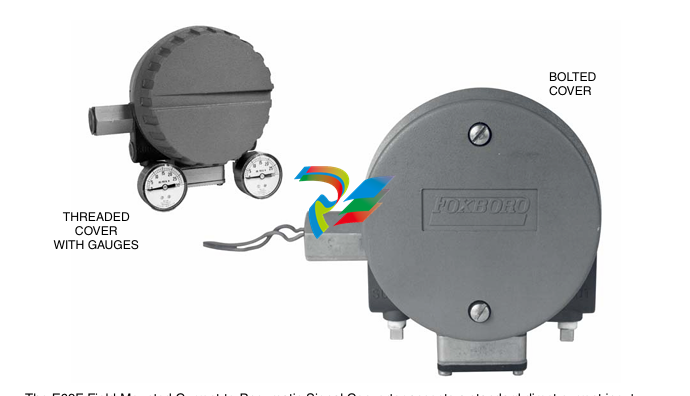
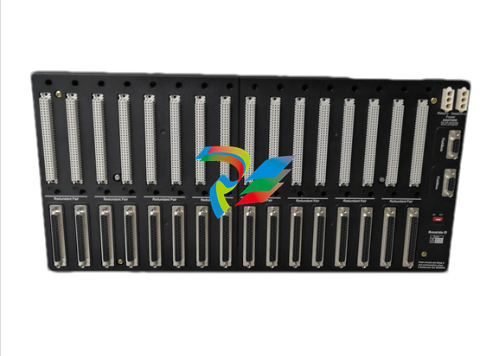
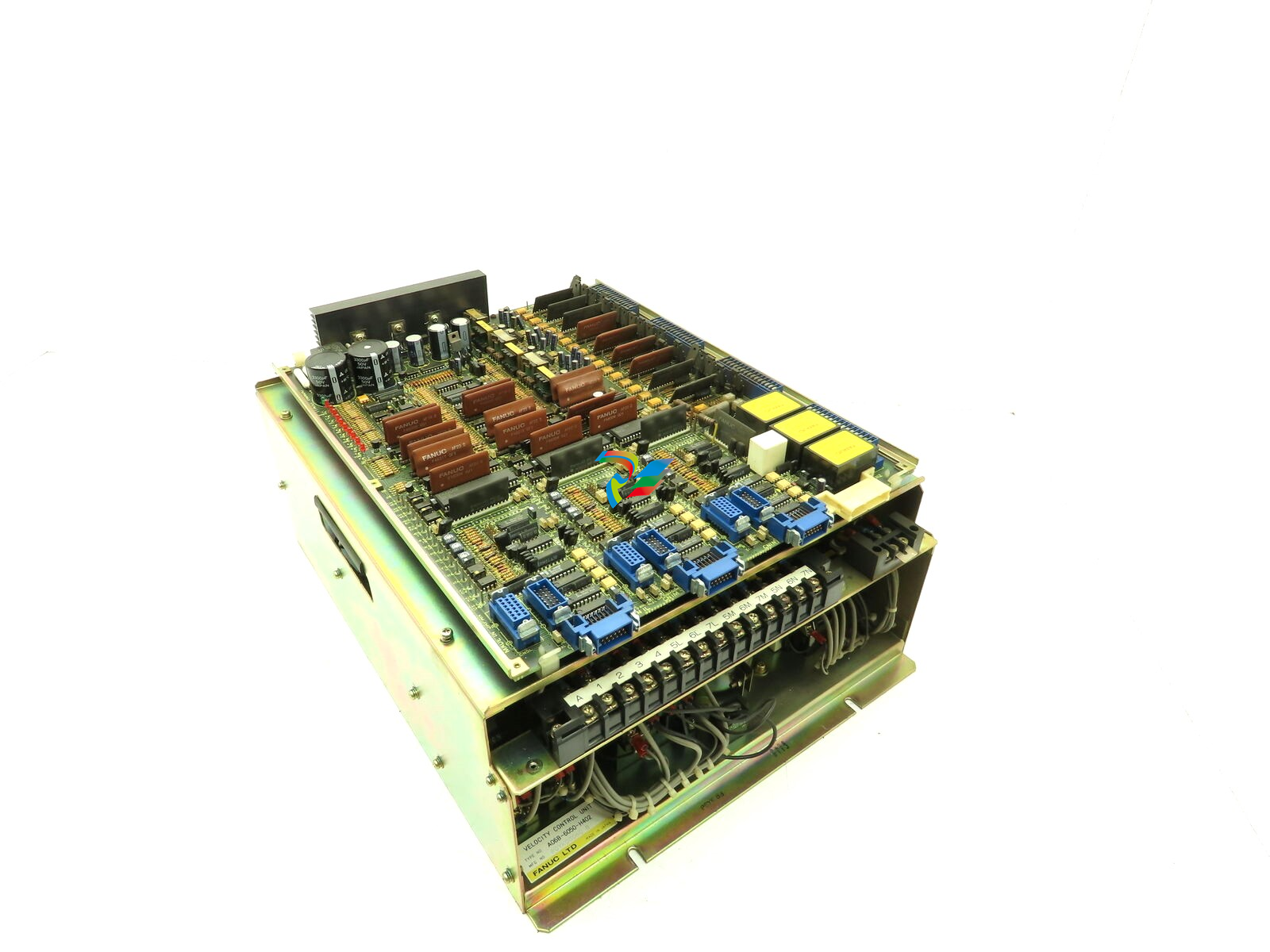
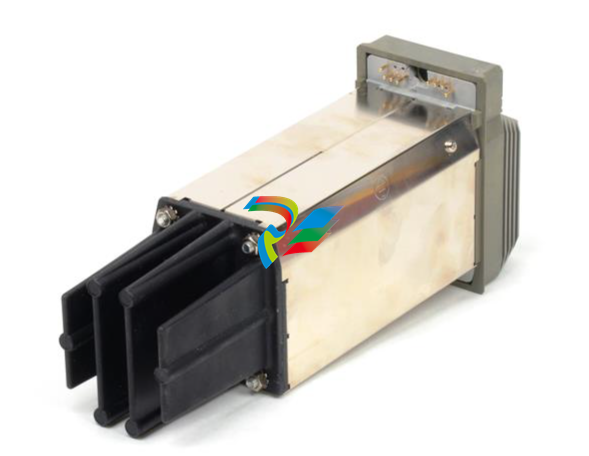
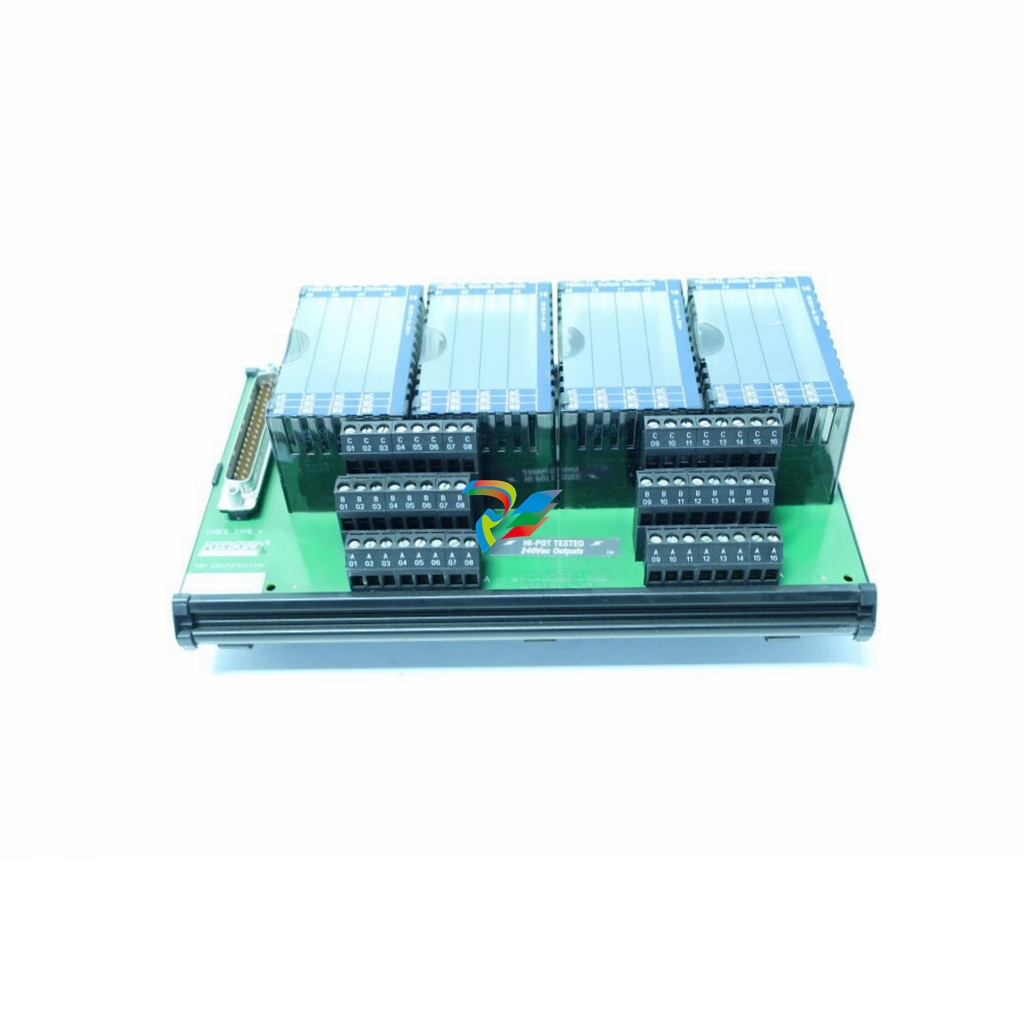
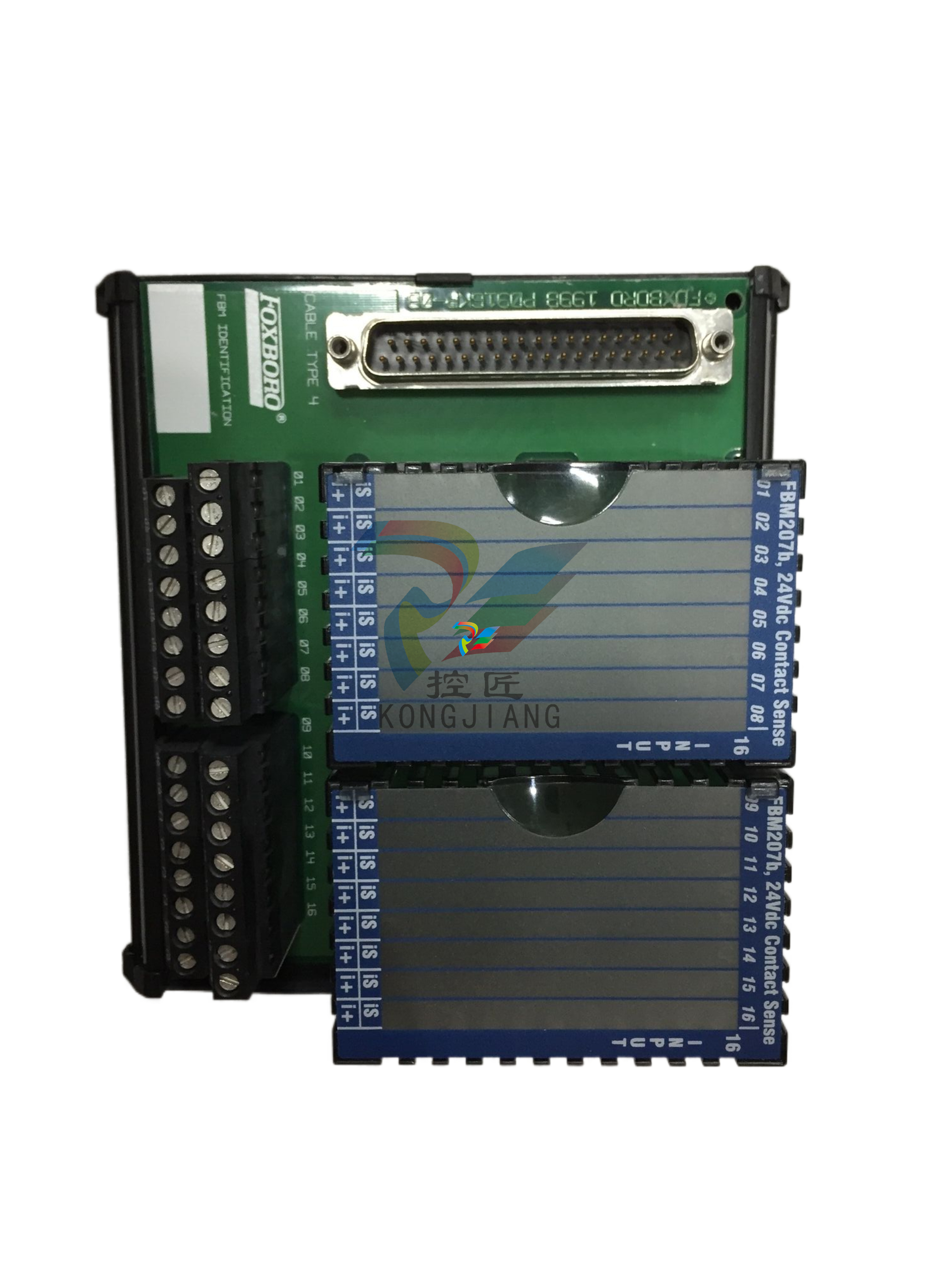
Importance of backups: Maintaining backups is essential because every environment experiences downtime. This downtime may result from cyberattacks, human error, or environmental issues. Organizations must ensure they have the latest backups to restore configuration files for OT equipment such as remote terminal units (RTUs), programmable logic controllers (PLCs), computer numerical control (CNC) machines and laser cutters. The effort to maintain backups is minimal, but the rewards are significant. Having up-to-date backups allows OT systems to quickly resume their critical functions after a disruption.
Asset inventory or comprehensive OT configuration management database (CMDB): Quite a few large companies lack a comprehensive understanding of their OT environment. They do not know all the different equipment or their network connections. It is crucial to document all OT equipment, whether connected to the network or air-gapped. At a minimum, collect data on the model, make, industrial purpose, technical point of contact, network connectivity, engineering workstation connections and human-machine interface (HMI) connections. This data is crucial for understanding the environment and establishing an incident response program. Depending on the CMDB tool used, it can also serve as the central repository for backups.
Implement a security framework: Establishing a cybersecurity program is straightforward with multiple available frameworks. These frameworks help organizations understand what they need to implement for better cybersecurity posture and maturity. The NIST Cybersecurity Framework, for example, is industry-agnostic and allows organizations to map out their cybersecurity program against recommended guidelines. Evaluating an organization against a suitable framework helps identify gaps in the cybersecurity program. The cost is minimal, requiring resources to communicate across the organization to understand the current posture. In addition, the ISA/IEC 62443 series of standards is also a useful tool to help manufacturers and asset owners start and then continue to grow their security programs.
Maintain basic hygiene: Regular software updates, patch management and strong password policies are fundamental. Ensuring these basic hygiene practices are in place can prevent a significant number of attacks.
Secure remote access: During COVID-19, remote access to OT environments surged. Organizations realized cost savings by having vendors remotely troubleshoot and monitor equipment for efficiency and warranty support. However, in the rush to quickly ensure remote access at the time, security professionals delayed implementing precautions until later—and quite a few organizations suffered the consequences. What the industry learned is secure remote access is more important now than it has ever been. Network segmentation helps implement secure remote access programs. With network segmentation, companies can restrict vendors to specific assets and prevent remote access OT devices from interacting with other parts of the network.
Beyond the basics
While applying basic OT cybersecurity practices can alleviate the majority of attacks, Chowdhury said that there are also new technologies that can help address sophisticated cyberattacks. “Implementing fundamental actions


































.jpg)
.jpg)
.jpg)




.jpg)


.png)
.jpg)
.jpg)
_lVjBYb.jpg)

.jpg)
.jpg)



.jpg)
.jpg)







.jpg)

.jpg)
.jpg)








.jpg)



.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)

.jpg)
.jpg)
.jpg)



.jpg)


.jpg)